Cyberspace is quite a dangerous place today. More and more people are moving into the digital world by voluntarily uploading data online, and criminals are trying to exploit it. This makes cybersecurity one of the most pressing challenges that corporations are facing. Unknown cybercriminals exploit vulnerabilities in computer systems to disrupt services and steal confidential information.
No matter the scope of your business, you can’t ignore cybersecurity threats. While there are a lot of ways to mitigate such threats, IT giants are widely relying on one technology in particular: machine learning (ML).
Machine learning has come into the limelight, as it is a technology that changes the notion of cybersecurity. One of the broadest definitions states that machine learning is a subfield of artificial intelligence that is characterized by the machine’s ability to imitate intelligent human behavior. These systems aren’t explicitly programmed to do this; instead, they use large data sets and training algorithms to learn more patterns and get more insights.
This means that between artificial intelligence and machine learning lies one of the largest hierarchical relationships, all built upon digital analogs of the patterns of how people think.
Many companies successfully use top machine learning technologies in their operational activity to be able to collect, organize, and analyze the right information. The underlying data gives them a complete picture of the environment and serves as the key to the effective implementation of such algorithms. So, the simple truth is that ML is a must for success in modern business reality.
In this article, we will overview how PayPal, Visa, IBM, Google, and others are implementing ML to improve cybersecurity.
- 1. Why Cybersecurity Issues Are Important
- 1.1. What Is a Cyberattack?
- 1.2. The Impact of Cyber Attacks
- 1.3. Principles of Cyber Security
- 2. Success Stories of Big Technology Companies Using ML
- 2.1. Machine Learning and Cybersecurity
- 2.2. Advantages of Machine Learning
- 2.3. Top List of Reasons You Should Use ML in Cybersecurity
- 2.4. Big Technology Companies Using ML in Cybersecurity
- Things You Need to Consider Before Implementation
Why Cybersecurity Issues Are Important
We are living in the digital era. After all, more and more activities can be implemented online, and the associated infrastructure is becoming increasingly complex. All these systems are vulnerable to a wide range of new risks coming from various sources. It makes their protection from cyberattacks a top priority.
What Is a Cyberattack?
A cyberattack is an attack implemented via cyberspace that aims to disrupt, disable, destroy, or maliciously control a computing infrastructure. Cyberattacks result in data breaches and information theft. All these aspects make this type of crime a serious threat for everyone: individuals, businesses, and even governments. No matter what the source of cyberattacks is (either from hacker groups or cyber warfare units sponsored by states and governments), they are becoming a reason for serious concern, as they are happening daily and their number is only growing. John Chambers, the former Cisco CEO, once said, “There are two types of companies: those that have been hacked and those who don’t yet know they have been hacked.”
A cyberattack is a complex phenomenon with its own classification. To understand that, we’ve gathered every aspect of this process. So, the most widespread types include the following.
- A malware attack occurs when some malicious software executes unauthorized computer algorithms on the potential victim’s system. The subtypes of malware include ransomware, spyware, command and control, and pre-analyzed behavior models. Malware breaks into the system through a vulnerability at the moment when a user is clicking the link that looks familiar and, as a result, safe or is opening an attachment from the incoming e-mail. After getting into the system, malware can be quite harmful. It can block access to some crucial components, transmit confidential data from the drive, install spy software, and even make the whole system inoperable. You probably know that, sometimes, just a click from one user can roll all the work of your software engineers back to the 90s. And we know solutions that will help your industry — this will be discussed below.
- Phishing attacks are becoming increasingly popular. They are usually implemented in combination with some social engineering techniques — typically, a cybercriminal deceives the victim and sends fraudulent communications that look like ones from reliable sources. One of the conditions for success is getting access to confidential information like logins and passwords or installing some malicious software on the system that is being hacked.
- Denial of service (DoS) attacks are used to attack a system, network, or server by flooding it with heavy, malicious traffic. The main goal is to make the system inoperable and unable to fulfill any requests. One subtype is the distributed DoS attack, in which many compromised devices are used.
- Man-in-the-middle (MitM) attacks, or eavesdropping attacks, occur when a hacker becomes the third party in a two-party transaction. When this happens, the attackers are able to interrupt the traffic and filter and steal data. In some MitM attacks, cybercriminals take advantage of unsecured public WiFi; they insert themselves between the network and a connected device. In other attacks, the hacker installs malicious software on the device itself to get access to the user’s data.
- A Structured Query Language (SQL) injection is an attack in which a hacker inserts malicious code into a database using SQL query and makes it reveal confidential data that it normally would not. SQL injections can be simply carried out by submitting code into a vulnerable search box on the website.
- Zero-day exploits occur when a network vulnerability is not discovered for a long time (or it’s known but ignored — whatever you like), but a solution is not yet implemented. That is why this type of attack is time-sensitive and requires constant attention.
The number of types of cyberattacks is growing (from social media spam and intrusive chatbots even to using human voice search algorithms in natural language processing), and these are just the most common. The reasons behind cybercrimes may be different. Most of the attackers want to benefit from vulnerabilities in business systems in order to steal confidential data about us or our money. Sometimes the motives can be ulterior or personal. Some hackers call themselves “hacktivists” and aim to disrupt corporate systems and governments.
The Impact of Cyber Attacks
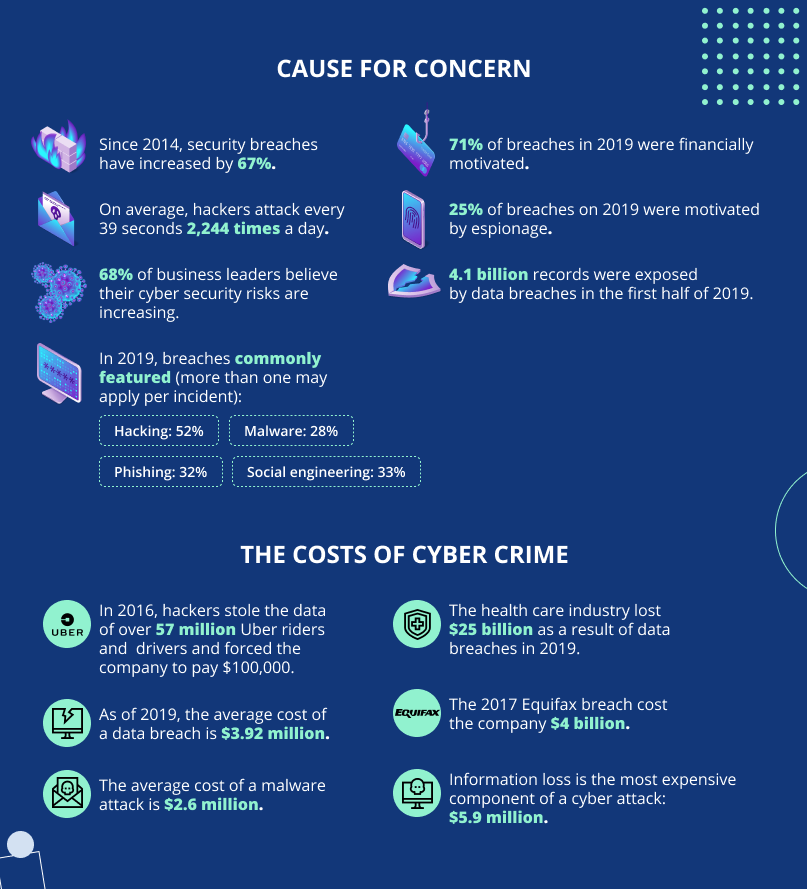
In any case, cyberattacks are threats that can have a negative impact on many aspects of business activity. The security breaches that are used by the hackers can lead to financial losses, reputational damage, and legal consequences.
- The economic cost of a cyberattack includes the theft of confidential information, financial data, money, disruptions in trading activity, and the loss of contracts and other business agreements. It also costs money to restore the affected systems.
- Reputational damage is hard to assess from a financial point of view, but it is highly likely to decrease the amount of trust that the customers had for the business. It, in turn, leads to reduced sales and profits.
- Legal consequences are the third important risk, as data protection and management are regulated by law. If the data is compromised somehow because of inappropriate security measures, fines and regulatory sanctions may easily occur.
Principles of Cyber Security
Effective cyber security is built on the basis of several important principles that are designed to protect systems and networks from attacks in cyberspace. These principles include:
- Risk management plan
- Secure configuration
- Network security
- Management of user rights
- User awareness
- Incident analysis
- Malware prevention
- Constant monitoring
- Implementing ML solutions
Success Stories of Big Technology Companies Using Machine Learning
Big technology companies were some of the first entities that understood the importance of implementing ML algorithms for the sake of cybersecurity. This led to the situation we are having now: the business world is heavily reliant upon ML systems.
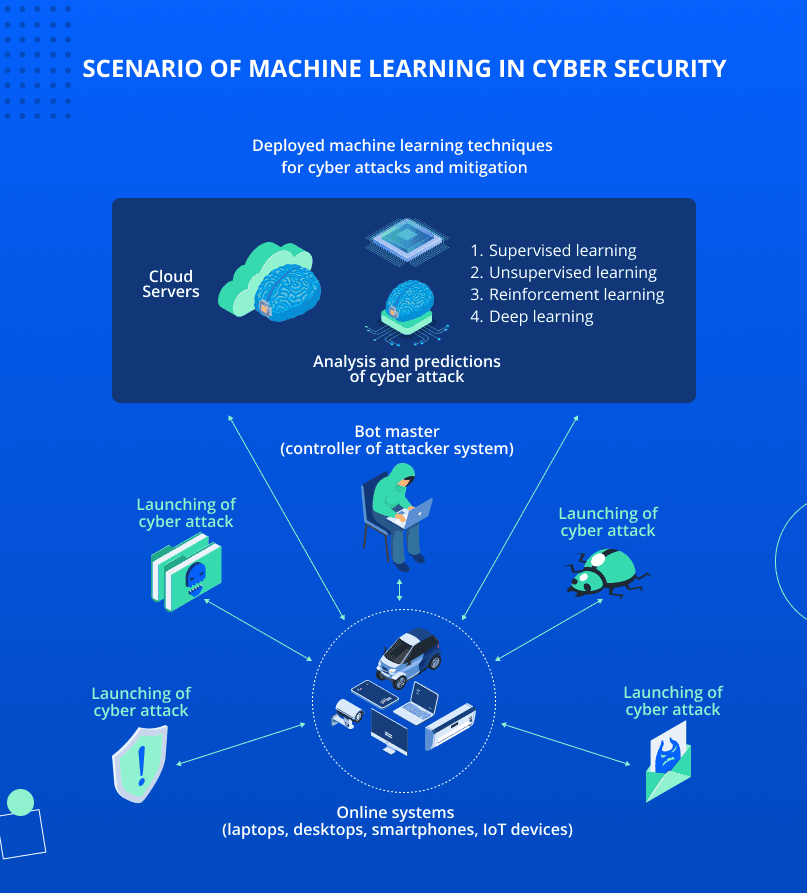
Machine Learning and Cybersecurity
Machine learning’s main role as a technology is to help your organization improve cybersecurity positions in three main ways.
- Anomaly detection. ML algorithms analyze behavioral patterns. They use many continuously evolving parameters to detect anomalies that may point to possible attacks.
- Future data breach prediction. ML algorithms are able to process and assess Big Data of various types to predict cyber-attacks before they occur.
- Data breach responses in real-time. It’s an AI and ML algorithm that sends notifications and alerts once a cyber-attack is detected. Some can even respond autonomously without human involvement by immediately and automatically security patches.
Advantages of Machine Learning
The benefits that ML implementation gives to organizations are really substantial and include:
- Increased speed of attack detection and responses. This is because ML algorithms can analyze massive data sets in very short timeframes. They play a crucial role in cybersecurity, especially when new types of cyberattacks can quickly penetrate corporate infrastructure.
- Lower IT costs. ML algorithms need much less effort to detect and protect infrastructure from cyber threats compared to manual responses. That makes the observed technology very cost-effective.
- Increased effectiveness of cyber-analysts. ML technology reduces the workload for IT specialists thanks to its ability to automatically sift through data logs. With a constant and comprehensive data science approach, cyber-analysts can be better prepared for the most complex threats.
- Improvement of overall security. The more data is analyzed, the more secure the system is, as ML is improving upon past patterns.
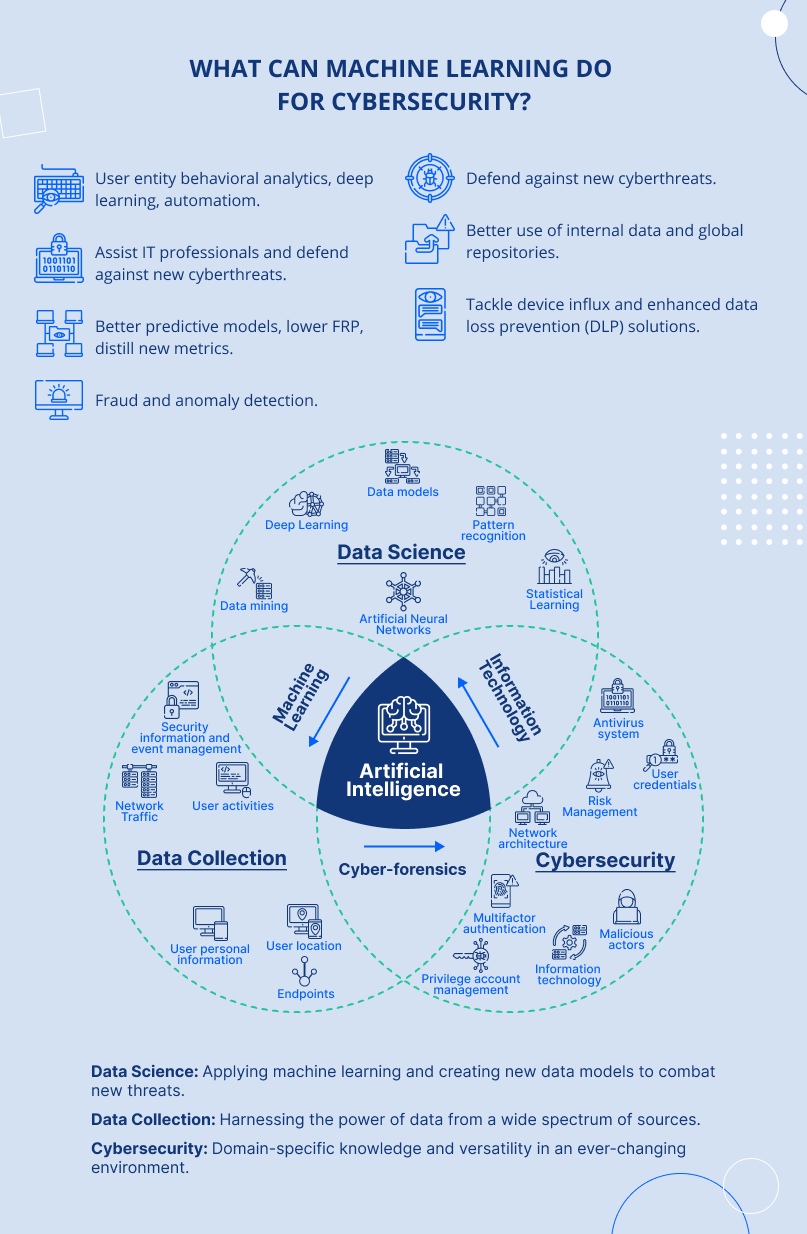
Top List of Reasons You Should Use Machine Learning in Cybersecurity
Machine learning is not perfect, but this technology is expected to become much more effective in the near future. Some of its successful applications include:
- Ranking network risks. Many corporations use ML to rank the risks that might be faced. The algorithms analyze the risks, define the most destructive ones, detect the most vulnerable parts of the infrastructure, and distribute the resources accordingly.
- Rapid detection of intrusions. Corporations use ML to get access to insights into malicious activity and detect threats as soon as they occur.
- Identification of suspicious behavior. ML is able to pinpoint unusual user behavior. Tracking suspicious actions helps to distinguish normal patterns from aberrant ones that may imply cyber threats. It makes responding to them even faster.
- Detection of fraud. Through its ability to recognize out-of-the-ordinary customer behavior features, top machine learning applications help financial organizations detect possible fraud even before they occur, leading to less financial loss.
- Malware discovery. ML is able to predict future malware infections on the basis of patterns that were discovered in previous malware.
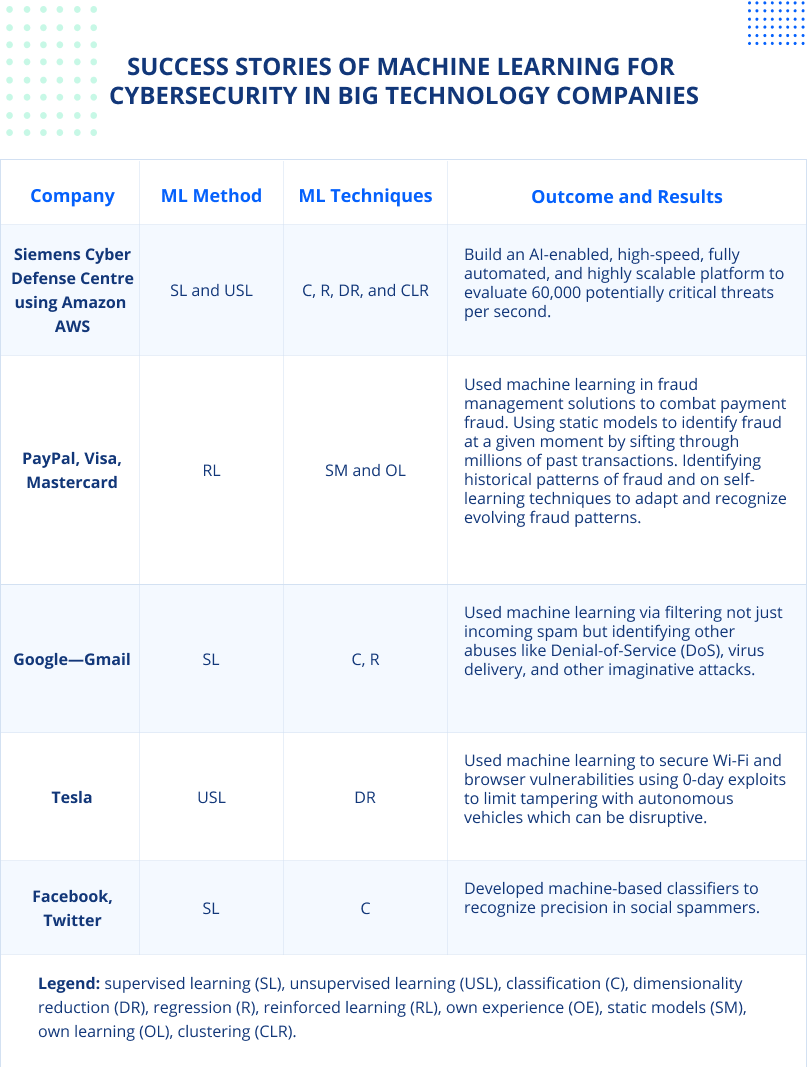
Big Technology Companies Using Machine Learning in Cybersecurity Cases
The number of companies that successfully implement ML algorithms and advanced capabilities of AI systems is constantly growing. Let’s have a look at some interesting cases.
PayPal
PayPal is one of the global leaders in the implementation of ML systems. The tech company has used its vast transaction data from 350 million consumers in 200 markets to create an artificial intelligence engine with the ultimate goal of preventing fraud and reducing the number of false alarms produced by older versions of the software.
You can look back a few years to when PayPal’s ML algorithms became capable of handling different scenarios of modern user behavior and detecting the fraud patterns that try to imitate it. Huge data sets with multiple variables were processed to find correlations practically in real-time. Training these models with millions of good and bad examples helped them to identify bad buying habits independently.
At the dawn of its appearance, this startup earned a name for itself thanks to its ML algorithms. These algorithms also help check whether an individual is a legitimate user by assessing information like their device, phone number, email, IP address, and transaction data. Something unusual like a large number of login attempts may be considered a high-risk activity.
Visa
Visa uses ML to protect its clients with effective solutions. The algorithm analyzes such aspects as the likelihood of customers to travel in the next 1-3 months, the top destinations they are highly likely to choose, and the places where they are ready to use their cards.
Data for assessment comes from such sources as Visa’s global processing network. That provides a great number of variables like total spending, spending frequency, average transaction price, and so on. This information is used to create predictive behavioral models that will help detect fraud.
Mastercard
Mastercard’s Decision Management Platform is used to detect fraud at a really fast pace – 1.2 billion transactions are processed daily. This platform is built based on 13 different algorithms, which include neural networks, case-based reasoning, and, of course, ML. Such a complex solution is not only able to analyze all types of variables within one transaction but also to pinpoint how and why it happens. This helps the system understand whether a transaction is fraudulent or just a parent trying to buy something for a child.
IBM Watson
IBM also offers its own solutions for cybersecurity based on ML. They include:
- Cognitive security, which is a combination of artificial and human intelligence.
- Security SOAR, which is used to automate time-consuming, repetitive, and complex responses without human intervention.
- MaaS360 Advisor, which gives access to cognitive insights, image recognition, algorithms for voice systems, contextual analytics, and benchmarking in order to assess security events.
IBM Watson’s cases of cybersecurity implementation include, for example, Wimbledon, which has partnered with IBM Security to get digital presence protection from all types of threats during its tournament.
Google has declared itself a ML company. It means that it applies relevant algorithms not only to make sure its most popular services work properly but also to ensure they are safely utilized. The IT giant has a comprehensive approach to its protection policy, and we can applaud how it’s using ML to detect and analyze threats against Android devices and delete malware from them. It also uses ML as part of the security process and confirms that the number of scanned Gmail attachments exceeds 300 billion weekly. So, your application that Google programmers may provide you is as safe as your Swiss bank account — don’t doubt it.
Amazon Web Services
Amazon Web Services is one more service that offers solutions built upon ML. For example, one of its solutions is CodeGuru Reviewer, a developer tool that helps detect critical issues and security vulnerabilities.
Tesla
Security issues are becoming much more important regarding autonomous vehicles developed by tech companies like Tesla. ML algorithms can enhance the security of such vehicles. Data analytics collect ambiguous patterns (like wrong estimations of Social Value Orientation (SVO) by vehicles’ AI) for further investigation; this helps the system detect malware activities and unusual behavior of the vehicle in the future. This approach enhances the technologies that assist the driver and helps prevent accidents.
Meta and Twitter
These two companies deal with huge sets of their customers’ personal data that must be protected according to the laws of practically every country. ML algorithms are used to prevent stealing and the misuse of this data, to spot critical security flaws, and to protect users from unacceptable content.
Siemens
Siemens uses different solutions to fight crimes in cyberspace. For example, one of the Siemens affiliates, Siemens Energy, launched a solution to monitor and respond to threats against the Industrial Internet of Things (IIoT) in order to mitigate the risks that network creation brings. This solution is Eos.ii — a ML Security Information and Event Management (SIEM) platform that “provides CISOs with an evergreen foundation for industrial IoT security.” The platform collects data from endpoints for further analysis and insight creation — all this is implemented in one interface. What’s more, Eos.ii prioritizes high-impact events and alerts users about them.
Things You Need To Consider While Implementing Machine Learning for Cybersecurity
The advantages of using ML algorithms for cybersecurity are quite obvious: almost immediate response to threats, timely prediction of attacks, and risk mitigation. This leads to more sustainable business models and increased cost-effectiveness. The development of such solutions is leading to a safer space for conducting business.
ML algorithms have many aspects that are vital when it comes to their implementation for cybersecurity. Choosing the right algorithms depends on many factors like the volume, quality, and diversity of data. Understanding which solutions your business needs is also important. You should also pay attention to the accuracy and speed of the results. Only a combination of all these factors will make ML effective and successful.
Sometimes, even the most experienced cyber specialists are unable to say which ML algorithm is best suited for a particular task. In order to make the right choice, it is necessary to conduct experiments, try different combinations, and compare results.
A qualified team is of utmost importance for the successful deployment of ML. We at Jaydevs have all the necessary expertise and a portfolio of implemented projects.